Archive for October 2015
How do you know your computer is infected and its precaution.
There is no particular way to identify that your computer has been infected with malicious code. Some infections can completely destroy files and shut down your computer, while others can only affect your computer’s normal operations.
Be aware of any unusual or unexpected behaviors. If you are running anti-virus software, it may alert you that it has found malicious code on your computer. The anti-virus software may be able to clean the malicious code automatically, but if it can’t, you will need to take additional steps.
What can you do if you are infected?
 Minimize the damage :- If you are at work and have access to an IT department, contact them immediately. The sooner they can investigate and clean your computer, the less damage to your computer and other computers on the network. If you are at your home computer or a laptop, disconnect your computer from the internet. By removing the internet connection, you prevent virus from being able to access your computer and perform tasks such as locating personal data, manipulating or deleting files, or using your computer to attack other computers.
Minimize the damage :- If you are at work and have access to an IT department, contact them immediately. The sooner they can investigate and clean your computer, the less damage to your computer and other computers on the network. If you are at your home computer or a laptop, disconnect your computer from the internet. By removing the internet connection, you prevent virus from being able to access your computer and perform tasks such as locating personal data, manipulating or deleting files, or using your computer to attack other computers.
Remove the malicious code:- If you have anti-virus software installed on your computer, update the virus definitions (if possible), and perform a manual scan of your entire system. If you do not have anti-virus software, you can purchase it at a local computer store . If the software can’t locate and remove the infection, you may need to reinstall your operating system, usually with a system restore disk that is often supplied with a new computer. Note that reinstalling or restoring the operating system typically erases all of your files and any additional software that you have installed on your computer. After reinstalling the operating system and any other software, install all of the appropriate patches to fix known vulnerabilities.
How can you reduce the risk of another infection?
Dealing with the presence of malicious code on your computer can be a bad experience that can cost you time, money, and data. The following recommendations will build your defense against future attacks:-
Use and maintain anti-virus software – Anti-virus software recognizes and protects your computer against most known viruses. However, attackers are continually writing new viruses, so it is important to keep your anti-virus software current .
Change your passwords – Your original passwords may have been compromised during the infection, so you should change them. This includes passwords for web sites that may have been cached in your browser. Make the passwords difficult for attackers to guess .
Keep software up to date – Install software patches so that attackers can’t take advantage of known problems or vulnerabilities . Many operating systems offer automatic updates. If this option is available, you should enable it.
Install or enable a firewall – Firewalls may be able to prevent some types of infection by blocking malicious traffic before it can enter your computer . Some operating systems actually include a firewall, but you need to make sure it is enabled.
Use anti-spyware tools – Spyware is a common source of viruses, but you can minimize the number of infections by using a legitimate program that identifies and removes spyware.
Follow good security practices – Take appropriate precautions when using email and web browsers so that you reduce the risk that your actions will trigger an infection .
15 Top-Paying Certifications for 2015
 To gain refined skills and expertise and to increase pay, many IT professionals choose to pursue a certification.
To gain refined skills and expertise and to increase pay, many IT professionals choose to pursue a certification.
Certifications in IT security, networking, and systems management are at the top of the certification pay scale. What may surprise you are the business-related certifications holding their own on this year's list.
The IT Skills and Salary Survey is a nationwide survey. Variations exist based on respondents' work location, years of experience, and company type (government, nonprofit, etc.).
1. Certified in Risk and Information Systems Control (CRISC)
The nonprofit group ISACA offers CRISC certification, much in the way that CompTIA manages the A+ and Network+ certifications. Formerly, "ISACA" stood for Information Systems Audit and Control Association, but now they've gone acronym only.
The CRISC certification is designed for IT professionals, project managers, and others whose job it is to identify and manage risks through appropriate Information Systems (IS) controls, covering the entire lifecycle, from design to implementation to ongoing maintenance. It measures two primary areas: risk and IS controls.This is not a case where you can just take a class and get certified. Achieving CRISC certification requires effort and years of planning.
2. Certified Information Security Manager (CISM)
ISACA also created CISM certification. It's aimed at management more than the IT professional and focuses on security strategy and assessing the systems and policies in place more than it focuses on the person who actually implements those policies using a particular vendor's platform.
It also requires at least five years of experience in IS, with at least three of those as a security manager. As with CRISC, requirements for CISM certification demand effort and years of planning.
3. Certified Information Systems Security Professional (CISSP)
Offered by the International Information Systems Security Certification Consortium (ISC)2, CISSP is designed to provide vendor-neutral security expertise, similar to the certifications ISACA offers.
Launched in 1994, CISSP consists of an exam based around ten different areas in computer security, including risk analysis, cloud computing, security when developing applications, mobile, cryptography, physical security, business continuity and disaster recovery planning, and legal and compliance issues.
4. Project Management Professional (PMP®)
The fourth highest paying and the first that is not security related, the PMP certification was created and is administered by the Project Management Institute (PMI®). It is the most recognized project management certification available. There are more than 630,000 PMPs worldwide.
The PMP certification exam tests five areas relating to the lifecycle of a project: initiating, planning, executing, monitoring and controlling, and closing. PMP certification is for running any kind of project, and it is not specialized into sub types, such as manufacturing, construction, or IT.
5. Certified Information Systems Auditor (CISA)
The fifth highest-paying certification is also from ISACA, and this one is for IS auditors. CISA certification is ISACA's oldest, dating back to 1978, with more than 106,000 people certified since its inception. CISA certification requires at least five years of experience in IS auditing, control, or security in addition to passing an exam that is only offered three times per year.
The CISA certification is usually obtained by those whose job responsibilities include auditing, monitoring, controlling, and/or assessing IT and/or business systems. It is designed to test the candidate's ability to manage vulnerabilities, ensure compliance with standards, and propose controls, processes, and updates to a company's policies to ensure compliance with accepted IT and business standards.
6. Microsoft Certified Systems Engineer (MCSE)
This certification ranked number 11 with an average salary of $96,121 for those who didn't list an associated Windows version and $96,726 for those who listed MCSE on Windows 2003, for the weighted average of $96,198 listed above.
The Microsoft Certified Systems Engineer is an old certification and is no longer attainable. It has been replaced by the Microsoft Certified Solutions Expert (yes, also MCSE). The Engineer certification was valid for Windows NT 3.51 - 2003, and the new Expert certification is for Windows 2012. There is an upgrade path if you are currently an MCSA or MCITP on Windows 2008. There is no direct upgrade path from the old MCSE to the new MCSE.
7. ITIL v3 Foundation
ITIL® was created by England's government in the 1980s to standardize IT management. It is a set of best practices for aligning the services IT provides with the needs of the organization. It is broad based, covering everything from availability and capacity management to change and incident management, in addition to application and IT operations management.
ITIL Foundation certification is the entry-level one and provides a broad-based understanding of the IT lifecycle and the concepts and terminology surrounding it. Anyone wishing for higher-level certifications must have this level first, thus people may have higher certifications and still list this certification in the survey, which may skew the salary somewhat.
8.Certified Ethical Hacker (CEH)
The International Council of E-Commerce Consultants created and manages CEH certification. It is designed to test the candidate's abilities to prod for holes, weaknesses, and vulnerabilities in a company's network defenses using techniques and methods that hackers employ.
The difference between a hacker and a CEH is that a hacker wants to cause damage, steal information, etc., while the CEH wants to fix the deficiencies found. Given the many attacks, the great volume of personal data at risk, and the legal liabilities possible, the need for CEHs is quite high, hence the salaries offered.
9.Cisco Certified Design Associate (CCDA)
Cisco's certification levels are Entry, Associate, Professional, Expert, and Architect. Those who obtain this Associate-level certification are typically network design engineers, technicians, or support technicians.
They are expected to design basic campus-type networks and be familiar with routing and switching, security, voice and video, wireless connectivity, and IP (both v4 and v6). They often work as part of a team with those who have higher-level Cisco certifications.
10.Cisco Certified Network Professional (CCNP) Routing and Switching
CCNP Routing and Switching certification is a follow on to Cisco Certified Network Associate (CCNA) Routing and Switching certification and a prerequisite to Cisco Certified Internetwork Expert (CCIE) Routing and Switching. Many CCNA-level engineers move on to CCNP Routing and Switching to show greater knowledge and depth in networking and to earn higher salaries.
CCNPs in routing and switching typically have at least a couple of years of experience (though that experience is not required) and have demonstrated the ability to plan, deploy, and troubleshoot both LAN and WAN scenarios and work with experts in related fields, such as voice and wireless. CCNP Routing and Switching certification requires separate exams in switching, routing, and troubleshooting.
Also Read ..
Top Ten Penetration Testing Linux Distributions
- ArchAssault
- Kali Linux
- BackBox
- BlackArch Linux
- Knoppix STD
- Pentoo
- Parrot Linux
- DEFT
- CAINE
- Samurai Web Testing Framework
- Matriux Krypton
- Cyborg Linux
- WEAKERTH4N
- Bugtraq
- NodeZero
- Fedora Security Spin
As of early 2012 BackTrack was used by over four million amateur and professional security researchers and professionals. Clearly it is extremely popular but there are other Linux pentesting distributions out there! Just like a good plumber needs his tools so does the budding pentester or curious hacker. Every information security professional needs to work with a penetration testing distro but also, most, if not all, training requires that you must use pentesting tools within a Linux Pentesting/ Forensics Box.
OK, none of the following Pentesting distributions were in the top 100 list over at Distro Watch but we don’t care – we are talking about penetration testing tools – or specifically the creation of distro’s that have all the necessary open source tools that help ethical hackers and penetration testers do their job. Like everything else when it comes to choices, every pentesting distro has its own pros, cons and specialty. Some distro for example are better at web application vulnerability discovery, forensics, WiFi cracking, reverse engineering, malware analysis, social engineering etc.
1. BackTrack 5r3
The mamma or best known of Linux pentesting distros. BackTrack has a very cool strapline: “The quieter you become, the more you are able to hear.” That just sounds cool….
The mamma or best known of Linux pentesting distros. BackTrack has a very cool strapline: “The quieter you become, the more you are able to hear.” That just sounds cool….
BackTrack is based on the ever-popular Ubuntu. The pentesting distro used to be only available within a KDE environment but Gnome become was added as an option with the release of BackTrack v5. For those working in Information Security or intrusion detection, BackTrack is one of the most popular pentesting distros that can run on a live CD or flash drive. The distribution is ideal for wireless cracking, exploiting, web application assessment, learning, or social-engineering a client.
Here is a list of some of the awesome tools available in BackTrack 5r3 (the latest release).
To identify Live Hosts:
dnmap – Distributed NMap
address6 – (which acts as a IPV6 address conversion)
dnmap – Distributed NMap
address6 – (which acts as a IPV6 address conversion)
Information Gathering Analysis (Social Engineering)
Jigsaw – Grabs information about company employees
Uberharvest – Email harvester
sslcaudit – SSL Cert audit
VoIP honey – VoIP Honeypot
urlcrazy – Detects URL typos used in typo squatting, url hijacking, phishing
Jigsaw – Grabs information about company employees
Uberharvest – Email harvester
sslcaudit – SSL Cert audit
VoIP honey – VoIP Honeypot
urlcrazy – Detects URL typos used in typo squatting, url hijacking, phishing
Web Crawlers
Apache_users – Apache username enumerator
Deblaze – Performs enumeration and interrogation against Flash remote end points
Apache_users – Apache username enumerator
Deblaze – Performs enumeration and interrogation against Flash remote end points
Database Analysis
Tnscmd10g – Allows you to inject commands into Oracle
BBQSQL – Blind SQL injection toolkit
* If you are interested in Database Security see our Hacker Halted summary here.
Tnscmd10g – Allows you to inject commands into Oracle
BBQSQL – Blind SQL injection toolkit
* If you are interested in Database Security see our Hacker Halted summary here.
Bluetooth Analysis
Blueranger – Uses link quality to locate Bluetooth devices
Blueranger – Uses link quality to locate Bluetooth devices
Vulnerability Assessment
Lynis – Scans systems & software for security issues
DotDotPwn – Directory Traversal fuzzer
Lynis – Scans systems & software for security issues
DotDotPwn – Directory Traversal fuzzer
Exploitation Tools
Netgear-telnetable – Enables Telnet console on Netgear devices
Terminator – Smart Meter tester
Htexploit – Tool to bypass standard directory protection
Jboss-Autopwn – Deploys JSP shell on target JBoss servers
Websploit – Scans & analyses remote systems for vulnerabilities
Netgear-telnetable – Enables Telnet console on Netgear devices
Terminator – Smart Meter tester
Htexploit – Tool to bypass standard directory protection
Jboss-Autopwn – Deploys JSP shell on target JBoss servers
Websploit – Scans & analyses remote systems for vulnerabilities
Wireless Exploitation Tools
Bluepot – Bluetooth honeypot
Spooftooph – Spoofs or clones Bluetooth devices
Smartphone-Pentest-Framework
Fern-Wifi-cracker – Gui for testing Wireless encryption strength
Wi-fihoney – Creates fake APs using all encryption and monitors with Airodump
Wifite – Automated wireless auditor
Bluepot – Bluetooth honeypot
Spooftooph – Spoofs or clones Bluetooth devices
Smartphone-Pentest-Framework
Fern-Wifi-cracker – Gui for testing Wireless encryption strength
Wi-fihoney – Creates fake APs using all encryption and monitors with Airodump
Wifite – Automated wireless auditor
Password Tools
Creddump
Johnny
Manglefizz
Ophcrack
Phrasendresher
Rainbowcrack
Acccheck
smbexec
Creddump
Johnny
Manglefizz
Ophcrack
Phrasendresher
Rainbowcrack
Acccheck
smbexec
2. NodeZero.
Like BackTrack, NodeZero is an Ubuntu based distro used for penetration testing using repositories so every time Ubuntu releases a patch for its bugs, you also are notified for system updates or upgrades. Node Zero used to be famous for its inclusion of THC IPV6 Attack Toolkit which includes tools like alive6, detect-new-ip6, dnsdict6, etc, but I think that these days BackTrack 5r3 also includes these tools.
Like BackTrack, NodeZero is an Ubuntu based distro used for penetration testing using repositories so every time Ubuntu releases a patch for its bugs, you also are notified for system updates or upgrades. Node Zero used to be famous for its inclusion of THC IPV6 Attack Toolkit which includes tools like alive6, detect-new-ip6, dnsdict6, etc, but I think that these days BackTrack 5r3 also includes these tools.
Whereas BackTrack is touted as being a “run-everywhere” distro, i.e. running it live, NodeZero Linux (which can also be run live) state that the distros real strength comes from a hard install. NodeZero, in their own words, believe that a penetration tester “requires a strong and efficient system [achieved by using] a distribution that is a permanent installation, that benefits from a strong selection of tools, integrated with a stable Linux environment. Sounds cool. Ever tried it? Let us know in the comments below.
3. BackBox Linux
BackBox is getting more popular by the day. Like BackTrack and NodeZero, BackBox Linux is an Ubuntu-based distribution developed to perform penetration tests and security assessments. The developers state that the intention with BackBox is to create a pentesting distro that is fast and easy to use. BackBox does have a pretty concise looking desktop environment and seems to work very well. Like the other distros BackBox is always updated to the latest stable versions of the most often used and best-known ethical hacking tools through repositories.
BackBox is getting more popular by the day. Like BackTrack and NodeZero, BackBox Linux is an Ubuntu-based distribution developed to perform penetration tests and security assessments. The developers state that the intention with BackBox is to create a pentesting distro that is fast and easy to use. BackBox does have a pretty concise looking desktop environment and seems to work very well. Like the other distros BackBox is always updated to the latest stable versions of the most often used and best-known ethical hacking tools through repositories.
BackBox has all the usual suspect for Forensic Analysis, Documentation & Reporting and Reverse Engineering with tools like ettercap, john, metasploit, nmap, Social Engineering Toolkit, sleuthkit, w3af, wireshark, etc.
4. Blackbuntu.
Yes, as the name clearly suggests, this is yet another distro that is based on Ubuntu. Here is a list of Security and Penetration Testing tools – or rather categories available within the Blackbuntu package, (each category has many sub categories) but this gives you a general idea of what comes with this pentesting distro: Information Gathering, Network Mapping, Vulnerability Identification, Penetration, Privilege Escalation, Maintaining Access, Radio Network Analysis, VoIP Analysis, Digital Forensic, Reverse Engineering and a Miscellaneous section. This list is hardly revolutionary but the tools contained within might be different to the other distros.
Yes, as the name clearly suggests, this is yet another distro that is based on Ubuntu. Here is a list of Security and Penetration Testing tools – or rather categories available within the Blackbuntu package, (each category has many sub categories) but this gives you a general idea of what comes with this pentesting distro: Information Gathering, Network Mapping, Vulnerability Identification, Penetration, Privilege Escalation, Maintaining Access, Radio Network Analysis, VoIP Analysis, Digital Forensic, Reverse Engineering and a Miscellaneous section. This list is hardly revolutionary but the tools contained within might be different to the other distros.
5. Samurai Web Testing Framework.
This is a live Linux distro that has been pre-configured with some of the best of open source and free tools that focus on testing and attacking websites. (The difference with Samurai Web Testing Framework is that it focuses on attacking (and therefore being able to defend) websites. The developers outline four steps of a web pen-test. These steps are incorporated within the distro and contain the necessary tools to complete the task.
Step 1: Reconnaissance – Tools include Fierce domain scanner and Maltego.
Step 2: Mapping – Tools include WebScarab and ratproxy.
Step 3: Discovery – Tools include w3af and burp.
Step 4: Exploitation – Tools include BeEF, AJAXShell and much more.
This is a live Linux distro that has been pre-configured with some of the best of open source and free tools that focus on testing and attacking websites. (The difference with Samurai Web Testing Framework is that it focuses on attacking (and therefore being able to defend) websites. The developers outline four steps of a web pen-test. These steps are incorporated within the distro and contain the necessary tools to complete the task.
Step 1: Reconnaissance – Tools include Fierce domain scanner and Maltego.
Step 2: Mapping – Tools include WebScarab and ratproxy.
Step 3: Discovery – Tools include w3af and burp.
Step 4: Exploitation – Tools include BeEF, AJAXShell and much more.
Of interest as well, the Live CD also includes a pre-configured wiki, set up to be a central information store during your pen-test.
The Samurai Web Testing Framework is a live Linux distro that focuses on web application vulnerability research and web pentesting within a “safe environment” – i.e. so you can ethical hack without violating any laws. This is a pentesting distro recommended for penetration testers who wants to combine network and web app techniques.
6. Knoppix STD.
This distro is based on Debian and originated in Germany. The architecture is i486 and runs from the following desktops: GNOME, KDE, LXDE and also Openbox. Knoppix has been around for a long time now – in fact I think it was one of the original live distros.
This distro is based on Debian and originated in Germany. The architecture is i486 and runs from the following desktops: GNOME, KDE, LXDE and also Openbox. Knoppix has been around for a long time now – in fact I think it was one of the original live distros.
Knoppix is primarily designed to be used as a Live CD, it can also be installed on a hard disk. The STD in the Knoppix name stands for Security Tools Distribution. The Cryptography section is particularly well-known in Knoppix.
7. Pentoo.
Pentoo is a security-focused live CD based on Gentoo. In their own words “Pentoo is Gentoo with the pentoo overlay.” So, if you are into Pentoo then this is the distro for you. Their homepage lists some of their customized tools and kernel, including: a Hardened Kernel with aufs patches, Backported Wifi stack from latest stable kernel release, Module loading support ala slax, XFCE4 wm and Cuda/OPENCL cracking support with development tools.
Pentoo is a security-focused live CD based on Gentoo. In their own words “Pentoo is Gentoo with the pentoo overlay.” So, if you are into Pentoo then this is the distro for you. Their homepage lists some of their customized tools and kernel, including: a Hardened Kernel with aufs patches, Backported Wifi stack from latest stable kernel release, Module loading support ala slax, XFCE4 wm and Cuda/OPENCL cracking support with development tools.
8. WEAKERTH4N.
This penetration distribution is built from Debian Squeeze and uses Fluxbox for its’ desktop environment. This pentesting distro is particularly well adjusted for WiFi hacking since it contains many Wireless tools. Here is a quick summary of WEAKERTH4N’s tool categories: Wifi attacks, SQL Hacking, Cisco Exploitation, Password Cracking, Web Hacking, Bluetooth, VoIP Hacking, Social Engineering, Information Gathering, Fuzzing, Android Hacking, Networking and Shells.
This penetration distribution is built from Debian Squeeze and uses Fluxbox for its’ desktop environment. This pentesting distro is particularly well adjusted for WiFi hacking since it contains many Wireless tools. Here is a quick summary of WEAKERTH4N’s tool categories: Wifi attacks, SQL Hacking, Cisco Exploitation, Password Cracking, Web Hacking, Bluetooth, VoIP Hacking, Social Engineering, Information Gathering, Fuzzing, Android Hacking, Networking and Shells.
9. Matriux Krypton.
This linux distro is, I believe, is the first security distribution based directly on Debian, (after WEAKERTH4N?) if I am wrong please comment below! There are 300 security tools to work, called “arsenals”. The arsenals allow for penetration testing, ethical hacking, system and network administration, security testing, vulnerability analysis, cyber forensics investigations, exploiting, cracking and data recovery. The last category, data recovery, doesn’t seem to be prevalent in the other distros.
This linux distro is, I believe, is the first security distribution based directly on Debian, (after WEAKERTH4N?) if I am wrong please comment below! There are 300 security tools to work, called “arsenals”. The arsenals allow for penetration testing, ethical hacking, system and network administration, security testing, vulnerability analysis, cyber forensics investigations, exploiting, cracking and data recovery. The last category, data recovery, doesn’t seem to be prevalent in the other distros.
10. DEFT.
The latest version is DEFT 7 which is based on the new Linux Kernel 3 and the DART (Digital Advanced Response Toolkit). This distro is more orientated towards Computer Forensics and uses LXDE as desktop environment and WINE for executing Windows tools under Linux. The developers, (based in Italy) hope that their distro will be used by the Military, Police, Investigators, IT Auditors and professional penetration testers. DEFT is an abbreviation for “Digital Evidence & Forensic Toolkit”
The latest version is DEFT 7 which is based on the new Linux Kernel 3 and the DART (Digital Advanced Response Toolkit). This distro is more orientated towards Computer Forensics and uses LXDE as desktop environment and WINE for executing Windows tools under Linux. The developers, (based in Italy) hope that their distro will be used by the Military, Police, Investigators, IT Auditors and professional penetration testers. DEFT is an abbreviation for “Digital Evidence & Forensic Toolkit”
11. CAINE
A reader to our blog suggested to add CAINE which we duly have. CAINE Stands for Computer Aided Investigative Environment, and like many information security products and tools – it is Italian GNU/Linux live distribution. CAINE offers a comprehensive forensic environment that is organized to integrate existing software tools that are composed as software modules, all displayed within a friendly graphical interface. CAINE states to have three objectives. These are, to ensure that the distro works in an interoperable environment that supports the digital investigator during the four phases of the digital investigation. Secondly that the distro has a user friendly graphical interface and finally that it provides a semi-automated compilation of the final forensic report. As you would likely expect, CAINE is fully open-source.
A reader to our blog suggested to add CAINE which we duly have. CAINE Stands for Computer Aided Investigative Environment, and like many information security products and tools – it is Italian GNU/Linux live distribution. CAINE offers a comprehensive forensic environment that is organized to integrate existing software tools that are composed as software modules, all displayed within a friendly graphical interface. CAINE states to have three objectives. These are, to ensure that the distro works in an interoperable environment that supports the digital investigator during the four phases of the digital investigation. Secondly that the distro has a user friendly graphical interface and finally that it provides a semi-automated compilation of the final forensic report. As you would likely expect, CAINE is fully open-source.
If anyone has used this please let us know.
12. Bugtraq
Bugtraq is another reader submitted pentesting distro. Based on the 26.6.38 kernel, this distro offers a really wide range of penetration and forensic tools. Like most of the others in this list, Bugtraq can hard-install of obviously run as a Live DVD or from a USB drive. Bugtraq claims to have recently configured and updated the kernel for better performance but also importantly so that it can recognize more hardware, including wireless injection patches pentesting. The team at Bugtraq seem solid because they are clearly making an effort to get the kernel to work with more hardware – something which the other distributions don’t always place enough importance.
Some of the special features included with Bugtraq include (as stated) an expanded range of recognition for injection wireless drivers, (i.e. not just the usual Alfa rtl8187), a patched 2.6.38 kernel and solid installation of the usual suspects: Nessus, OpenVAS, Greenbone, Nod32, Hashcat, Avira etc.
Unique to Bugtraq (as claimed on their site) is the ability to, or better said, ease, of deleting tracks and backdoors. Just by having read about Bugtraq I’m really glad that I can add this to the list because it just sounds like a job well done. If you are interested in any of the following pentesting and forensic categories, then do go and check out Buqtraq: Malware, Penetration Shield, Web audit, Brute force attack, Communication and Forensics Analytics, Sniffers, Virtualizations, Anonymity and Tracking, Mapping and Vulnerability detection.
Quick Summary: You can’t go wrong with any Ubuntu based distro. BackTrack does the job well but I guess, of course, it’s all personal – i.e. does the distro do the job for you? Every penetration tester needs a lean towards a particular tool or tool-set. Frankly they are all good, and it would be prudent to use several of these pentesting distros as live versions. For WiFi hacking then WEAKERTH4N is likely your better friend, whilst to stay within the law, use Samurai.
Bugtraq looks really good – the team behind it seems to have taken considerable time to tick all the boxes. Once we test it I’ll update the post.
Here is a list of other distros (which we think are still alive and kicking – please correct us if we are wrong).
Other Distro’s
Damn Vulnerable Linux (reader comment: more of an operating system for attacking purposes)
Hakin9 (an educational and training distro that you can use to play-along with when subscribing to the Hacking Magazine Hak9)
Helix
nUbuntu
Network Security Toolkit (NST)
OWASP Labrat
Frenzy
grml
Ophcrack
FCCU
OSWA Assistant
Russix
Chaox-NG
GnackTrack
Katana
Securix-NSM
Auditor
Damn Vulnerable Linux (reader comment: more of an operating system for attacking purposes)
Hakin9 (an educational and training distro that you can use to play-along with when subscribing to the Hacking Magazine Hak9)
Helix
nUbuntu
Network Security Toolkit (NST)
OWASP Labrat
Frenzy
grml
Ophcrack
FCCU
OSWA Assistant
Russix
Chaox-NG
GnackTrack
Katana
Securix-NSM
Auditor
And here is a list of distros that, regrettably, have passed on to Linux Heaven.
KCPentrix
Protech
FIRE
Arudius
INSERT
Local Area Security (LAS)
NavynOS
Operator
PHLAK
PLAC
SENTINIX
Talos
ThePacketMaster
Trinux
WarLinux
Whoppix
WHAX
HeX
Stagos FSE
SNARL
KCPentrix
Protech
FIRE
Arudius
INSERT
Local Area Security (LAS)
NavynOS
Operator
PHLAK
PLAC
SENTINIX
Talos
ThePacketMaster
Trinux
WarLinux
Whoppix
WHAX
HeX
Stagos FSE
SNARL
Top Ten Hacker Tools of 2015
List of top ten hacker tools of 2015
For Education Purposes Only ***
Every task requires a good set of tools.This because having right tools in hand one can save much of its energy and time.In the world of Cyber Hacking (“Cyber Security” formally) there are millions of tools which are available on the Internet either as Freewares or as Sharewares.
If you are security researcher, pentester or a system admin, you need to have this on your PCs/laptops to find the vulnerabilities and plug them. Redback Cyber Security Council (RISC) conducted an online poll to determine top ten hacking tools out of some of the famous ones. Here is the list which came out the winner on the poll.
1. Nmap: Network Mapper
Abbreviated as nmap is a versatile tool for Network Security, plus it is free and open source.It is largely used by network administrators for network discovery and security auditing. System admins use nmap for network inventory, determining open ports, managing service upgrade schedules, and monitoring host(A term used for “a computer on a network”) or service uptime. The tool uses raw IP packets in many creative ways to determine what hosts are available on the network, what services (application name and version) they offer,which type of protocols are being used for providing the services,what operating systems (and OS versions and possible patches) and what type and version of packet filters/ firewalls are being used by the target.
2. Metasploit:
A tool for exploiting (Utilising network weakness for making a “backdoor”) vulnerabilities (Weak Points) on Network. This tool is neither free nor open source. But when it comes to features offered it deserves the price it claims. The Metasploit Project is a hugely popular pentesting (penetration testing) or hacking tool that is used by cybersecurity professionals and ethical hackers. Metasploit is essentially a computer security project that supplies information about known security vulnerabilities and helps to formulate penetration testing and IDS testing.
3. Cain and Abel:
Cain & Abel is a password recovery tool that is mostly used for Microsoft Operating Systems. This popular hacking tool allows the user to seek the recovery of various kind of passwords by sniffing the network(capturing some of the data packets), cracking encrypted passwords using Dictionary, Brute-Force(Generation of hashes out of words and then comparison of encrypted hash with the generated one,this method takes less time than dictionary attack method) and Cryptanalysis attacks. Cain, as it is often referred to, can also record VoIP(Voice over IP protocol,used for making calls over using internet) conversations, decode hashed scrambled passwords, recover wireless network keys and more.It can crack various types of hashes including NTLM,MD2,MD5,SHA-1,SHA-2 and many more.These functionalities make Cain and Abel one of the best password recovery tool.
4. Angry IP Scanner:
Angry IP Scanner, also known as ‘ipscan’ is a freely available (open-source and cross-platform) hacking network scanner that is both fast and easy to use. The main purpose of this hacking tool is to scan IP addresses and ports to find open doors and ports. Worth noting that Angry IP Scanner also has a bunch of other uses as well. Common users of this hacking tool include network administrators and system engineers.
5.John The Ripper:
John the Ripper is a popular password cracking pentesting tool that is most commonly used to perform dictionary attacks. John the Ripper takes text string samples (from a text file, referred to as a wordlist, containing popular and complex words found in a dictionary or real passwords cracked before), encrypting it in the same way as the password being cracked (including both the encryption algorithm and key), and comparing the output to the encrypted string. This tool can also be used to perform a variety of alterations to dictionary attacks.Including Brute Force and Rainbow attacks.
6. THC Hydra:
Although often considered as yet another password cracker, THC Hydra is hugely popular and has a very active and experienced development team. Essentially THC Hydra is a fast and stable Network Login Hacking Tool that will use dictionary or brute-force attacks to try various password and login combinations against an log in page. This hacking tool supports a wide set of protocols including Mail (POP3, IMAP, etc.), Databases, LDAP(Lightweight Directory Access Protocol),SMB, VNC, and SSH(Secure Shell,used by VPN Softwares).
7. Burp Suite:
A pentesting tool,Burp Suite has several features that can help the penetration tester or ethical hacker. Two commonly used applications used within this tool include the ‘Burp Suite Spider’ which can enumerate and map out the various pages and parameters of a web site by examining cookies and initiates connections with these web applications, and the ‘Intruder’ which performs automated attacks on web applications.
8. Nessus Remote Security Scanner
Recently went closed source, but is still essentially free. Works with a client-server framework. Nessus is the worlds Nessus Remote Security Scanner most popular vulnerability scanner used in over 75,000 organizations world-wide. Many of the worlds largest organizations are realizing significant cost savings by using Nessus to audit business-critical enterprise devices and applications. (This tool is not in the Concise list)
9. Ettercap:
Ettercap has a huge following and is widely used by cyber security professionals. Ettercap works by placing the user’s network interface into promiscuous mode and by ARP poisoning(ARP : Address resolution protocol is used to determine a host’s MAC address (address of its Network Interface Card) by knowing its IP address. ARP poisoning is a process where a hacker gives wrong information of either its MAC or IP address to the network.) the target machines, i.e. facilitating a ‘Man In The Middle’ or MITM attack. Once successful Ettercap (and the hacker) can deploy various attacks on the victims. A popular feature about Ettercap is its’ ability to support various plugins.
10. Wapiti:
Wapiti has a very loyal following. As a pentesting tool (or framework) Wapiti is able to scan and detect hundreds of possible vulnerabilities. Essentially this Multi Purpose Hacker Tools can audit the security of web applications by performing “black-box” scans, i.e. it does not study the source code of the application but will scan the HTML pages of the application seeking scripts and forms where it can inject data.
If you have any favourite tool of your own which we have not mentioned in the article, kindly mention it in the comments so that we can include it in our next list.
XKEYSCORE: NSA Biggest Spy Tool Ever!
XKEYSCORE: The NSA’s most intrusive spying software you have never heard of
Collecting the metadata from user’s cell phones has been in the news lately. The expiration of the Patriot Act and passage of the USA Freedom Act have been touted as curbing the worst abuses of the NSA for spying on American citizens, but metadata collection is not the only weapon in the NSA arsenal and XKEYSCORE, a secret program for intelligence gathering, is exponentially more intrusive and effective in collecting data from anyone with an email address.
In an interview with The Guardian newspaper in 2013, Edward Snowden said, “I, sitting at my desk, could wiretap anyone, from you or your accountant, to a federal judge or even the president, if I had a personal email.”
This controversial statement caused major headaches within the American intelligence community and denials from politicians and government agency heads.
“He’s lying. It’s impossible for him to do what he was saying he could do,” countered Mike Rogers (R-Mich.) chairman of the House intelligence committee.
However, XKEYSCORE does just that. The program allows a user with access to an email address to collect data on that person across email, the internet and phone conversations. This data is stored for three to five days and the metadata collected is stored for an additional 30 to 45 days.
According to the Intercept, XKEYSCORE uses the fiber optic network to collect “pictures, documents, voice calls, webcam photos, web searches, advertising analytics traffic, social media traffic, botnet traffic, logged keystrokes, computer network exploitation (CNE) targeting, intercepted username and password pairs, file uploads to online services, Skype sessions and more.”
XKEYSCORE has been likened to Google for surveillance. You type in the search query, and the program will determine who and what has been sent about it. If within the collection time frame, that information is available to whoever is using the program.
Information about XKEYSCORE has been available for years, but the sheer amount of information that can be collected by the program is just now coming to light. As more documents are released from the Edward Snowden trove, the details of these intelligence programs show that the NSA and the American Government have kept the full truth of their surveillance activities secret.
HSB Study: 69% of Businesses Reported Being Hacked in the Last Year
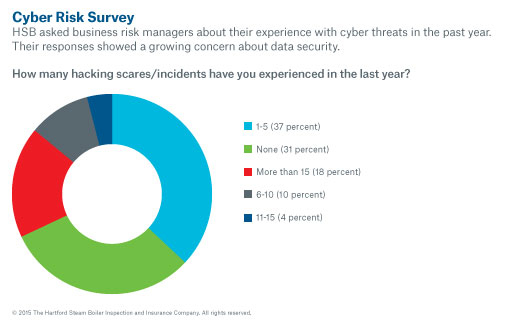
Almost 70 percent of businesses experienced at least one hacking incident in the last year, according to a study of business risk managers released by The Hartford Steam Boiler Inspection and Insurance Company (HSB), part of Munich Re. Yet, more than half (55 percent) don’t believe their company is dedicating enough money or trained and experienced personnel to combat the latest hacking techniques.
“Hackers have evolved and so have their methods of attack,” said Eric Cernak, Cyber Practice leader for Munich Re. “Businesses are on high alert, but they can do a lot better. Simply reacting to new threats is not enough. Businesses of all sizes need to anticipate hacking trends and deploy the resources necessary to protect their private or sensitive information.”
Of the 102 risk managers polled by HSB at the Risk and Insurance Management Society Conference (RIMS) in New Orleans this year, 63 percent represented large enterprises, followed by 30 percent at mid-sized organizations and seven percent at small businesses.
The survey revealed a notable exposure and concern with the use of cloud technology. Loss of confidentiality of information is viewed as the biggest risk (76 percent), followed by service interruption (16 percent) and government intrusion (5 percent).
Concerns about the type of information being breached ranged from personally identifiable information (53 percent) to sensitive corporate information (33 percent) to financial information (14 percent).
When asked about the type of risk management services they would be most interested in deploying to combat cyber risk, risk managers point to intrusion detection/penetration testing (32 percent), employee education programs (25 percent) and encryption (25 percent).
For additional protection, 46 percent say their business has either purchased cyber insurance for the first time or increased its level of coverage in the last year. Thirty-six percent of businesses do not have any level of cyber insurance coverage.
Hacking techniques!
1. Phishing
Phishing is still the most popular attack vector used for hacking Facebook accounts. There are variety methods to carry out phishing attack. In a simple phishing attacks a hacker creates a fake log in page which exactly looks like the real Facebook page and then asks the victim to log in. Once the victim log in through the fake page the, the victims "Email Address" and "Password" is stored in to a text file, and the hacker then downloads the text file and gets his hands on the victims credentials.
2. Keylogging
Keylogging is the easiest way to hack a Facebook password. Keylogging sometimes can be so dangerous that even a person with good knowledge of computers can fall for it. A Keylogger is basically a small program which, once is installed on victim's computer, will record every thing victim types on his/her computer. The logs are then send back to the attacker by either FTP or directly to hackers email address.
3. Stealer's
Almost 80% percent people use stored passwords in their browser to access the Facebook. This is quite convenient, but can sometimes be extremely dangerous. Stealer's are software's specially designed to capture the saved passwords stored in the victims Internet browser.
4. Session Hijacking
Session Hijacking can be often very dangerous if you are accessing Facebook on a http (non secure) connection. In Session Hijacking attack, a hacker steals the victims browser cookie which is used to authenticate the user on a website, and use it to access the victims account. Session hijacking is widely used on LAN, and WiFi connections.
5. Sidejacking With Firesheep
Sidejacking attack went common in late 2010, however it's still popular now a days. Firesheep is widely used to carry out sidejacking attacks. Firesheep only works when the attacker and victim is on the same WiFi network. A sidejacking attack is basically another name for http session hijacking, but it's more targeted towards WiFi users.
6. Mobile Phone Hacking
Millions of Facebook users access Facebook through their mobile phones. In case the hacker can gain access to the victims mobile phone then he can probably gain access to his/her Facebook account. Their are a lots of Mobile Spying software's used to monitor a Cellphone. The most popular Mobile Phone Spying software's are: Mobile Spy, and Spy Phone Gold.
7. DNS Spoofing
If both the victim and attacker are on the same network, an attacker can use a DNS spoofing attack and change the original Facebook page to his own fake page and hence can get access to victims Facebook account.
8. USB Hacking
If an attacker has physical access to your computer, he could just insert a USB programmed with a function to automatically extract saved passwords in the Internet browser.
9. Man In the Middle Attacks
If the victim and attacker are on the same LAN and on a switch based network, a hacker can place himself between the client and the server, or he could act as a default gateway and hence capturing all the traffic in between.
DDoS Attacks Jump by a Third in Q2
The volume of distributed denial of service (DDoS) attacks in Q2 increased by almost a third (32%) on the previous quarter, according to the latest stats from security vendor Corero Network Security.
The firm’s Trends and Analysis report for the first half of the year revealed customers experienced on average 4.5 DDoS attacks per day in the second quarter.
However, the vast majority (95%+) were less than 10Gbps and lasted less than 30 minutes.
Corero claimed that the increase was driven by the growing availability of cheap DDoS attack tools including botnets which can be hired to launch anonymous attacks very easily.
It added that shorter attacks were being launched more often in a bid to circumvent legacy cloud DDoS scrubbing tools and in some cases distract IT teams while information-stealing malware is used to grab sensitive data.
Corero Networks CTO Dave Larson explained that the vast majority of DDoS vectors aren’t used to cause service outages in the traditional sense.
“Additionally, security teams are not always aware that there is a connection between DDoS and other forms of cyber-attacks or data exfiltration attempts, so statistics that track the association are only just emerging,” he told Infosecurity.
“Historically, DDoS has been known for the ‘denial of service’, as the acronym would indicate, however we are seeing DDoS being used as a ‘denial of security’ more frequently – taking down or profiling existing network security layers in order to carry out more malicious activity. A more recent and public example is Carphone Warehouse falling victim to DDoS as a distraction; subsequently the personal details of 2.4 million customers was breached.”
Larson warned IT managers who have not yet suffered a major DDoS attack not to be lulled into a false sense of security.
“Invest some time familiarizing yourself with the trends in the DDoS landscape and start looking more closely at lower-level activity within your environment,” he added.
“When a breach does happen, claiming you had never had an outage before and so you thought your protections were just fine is not going to be very convincing to your management. The online enterprise requires a proactive and real-time approach to dealing with the onslaught of DDoS attacks targeting their networks.”
Don’t Try To Hack Into Your Own Device, Govt Will Destroy It- Thanks to TPP
The landmark TPP deal allows a judicial review over violation of Digital Rights Management technologies and could lead to the destruction of your devices if found guilty.
Forget the good old days when the kids used to open up the electronics at their homes in quest of knowledge and sometimes even tweak the original to create a multi-purpose device. So, no more playing around with the gadgets, because if you are caught, your device would be seized and destroyed as per the recently signed Trans Pacific Partnership (TPP) agreement.
Wikileaks has released the official documents regarding the copyrights chapter which forbids anyone to circumvent the copyright and product infringement laws and thereby make changes in the original devices or proprietary technology (software/hardware) for any purpose. Such are called DRM or Digital Rights Management technologies.

Well, DRM was always there but what comes new with the TPP is that judicial authorities would have the authority to confiscate and order the destruction of such devices and products found to be involved in any such DRM violation.
TPP is touted as the 21st-century landmark for trade liberalization and hog around 40% of the world’s economy and had been pushed aggressively since many years. The agreement has already come under fire for favoring the corporates and stifling the rights of consumers. Similar penal laws have been adjudicated against the free-flowing information on Internet, again with an intent to smother small businesses and create a corporate monopoly.
Worst affected by these new developments will be the white-hat hackers as bypassing the manufacturer’s exclusive system and finding the zero-day vulnerabilities is their job. Even individuals who want to improvise their devices are prohibited. As in the case of the Internet copyright violations, the punishment is from a monetary fine to a term in jail.
Wikileaks has also the leaked the device-destroying proposal in the TPP back in 2014 as well. After a long slumber, the whistle blowing forum has revived itself and lately has been crowdfunding to offer bounty in order to get confidential government documents such as this one and the US bombings in Doctors Without Borders Hospital in Afghanistan few days back.